Here are Container security best practices in Docker. The best security feature in Docker is it isolates Containers and avoids container-to container communication.
It stores images inside the container. The Image is a replica of the Software-application. You can keep multiple images of current and previous versions. So it is easy to control versions. Below sections helps you to know how Docker maintains Security.
Docker Containers & Security
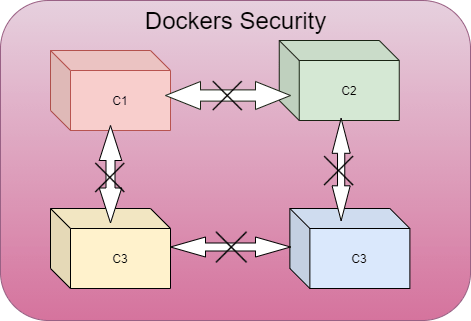
In the below picture, the Docker isolates each container. Further, a container can’t communicate with another container and even the host-operating system – except for storage volumes.
Security with Container Isolation
Though each container has separate processes, these are encapsulated in the Linux Kernel (Host Operating System). The most important is the central functions of the Linux kernel, such as Cgroups and namespaces. Here is an article more on Security.
The distribution of system resources (memory, CPU, bandwidth) takes place by means of a Cgroup mechanism that guarantees that each container can only consume the quota reserved for it.
Compared to Virtual Machine, the isolation in Docker is not much stricter. Due to this, an unauthorized attacker can spoil not only container data but also host operating systems’ Kernel.
Docker Security Vulnerabilities
The Os kernel is prone to security breach. The reason is it’s libraries communicate with Docker. So an attacker who breaks container can do for Kernel also.
Docker Security Best Practices & Tools
- A firewall is needed to stop attacking Host Os. You can achieve this by using the below frameworks:
- Restrict access to Daemon (which is the heart of Docker) to avoid security problems.
- The purpose of Registry is – it stores images, and you can pull them as well. So, safeguard the registry with the above frameworks.
Keep Reading








You must be logged in to post a comment.